Marketers still think email security is about hitting the inbox. It isn't. In 2026, your DNS config is a financial compliance vector. Miss a DMARC policy, and your payment gateway will freeze your merchant account. It is a mechanical certainty.
PCI DSS v4.0 shifted domain spoofing from an IT annoyance to a critical payment vulnerability. If your infrastructure leaks phishing emails, Stripe and PayPal will cut your cash flow to limit their liability. This is a breakdown of the exact sequence that turns a loose DNS record into a frozen bank account.

The 2026 Reality: Why Stripe and PayPal Care About Your DNS
For a decade, SPF and DKIM were treated as deliverability hacks. That ended with the PCI DSS v4.0 rollout. The standard now requires rigid anti-phishing and anti-spoofing controls for any entity touching payment data.
Payment processors do not care about your newsletter open rates. They care about risk exposure. If a bad actor can easily spoof your domain to send fraudulent invoices, your merchant account is flagged as a compromised asset. Gateway risk assessment algorithms now factor in domain authentication. If your infrastructure is open, you are a liability to the payment network.
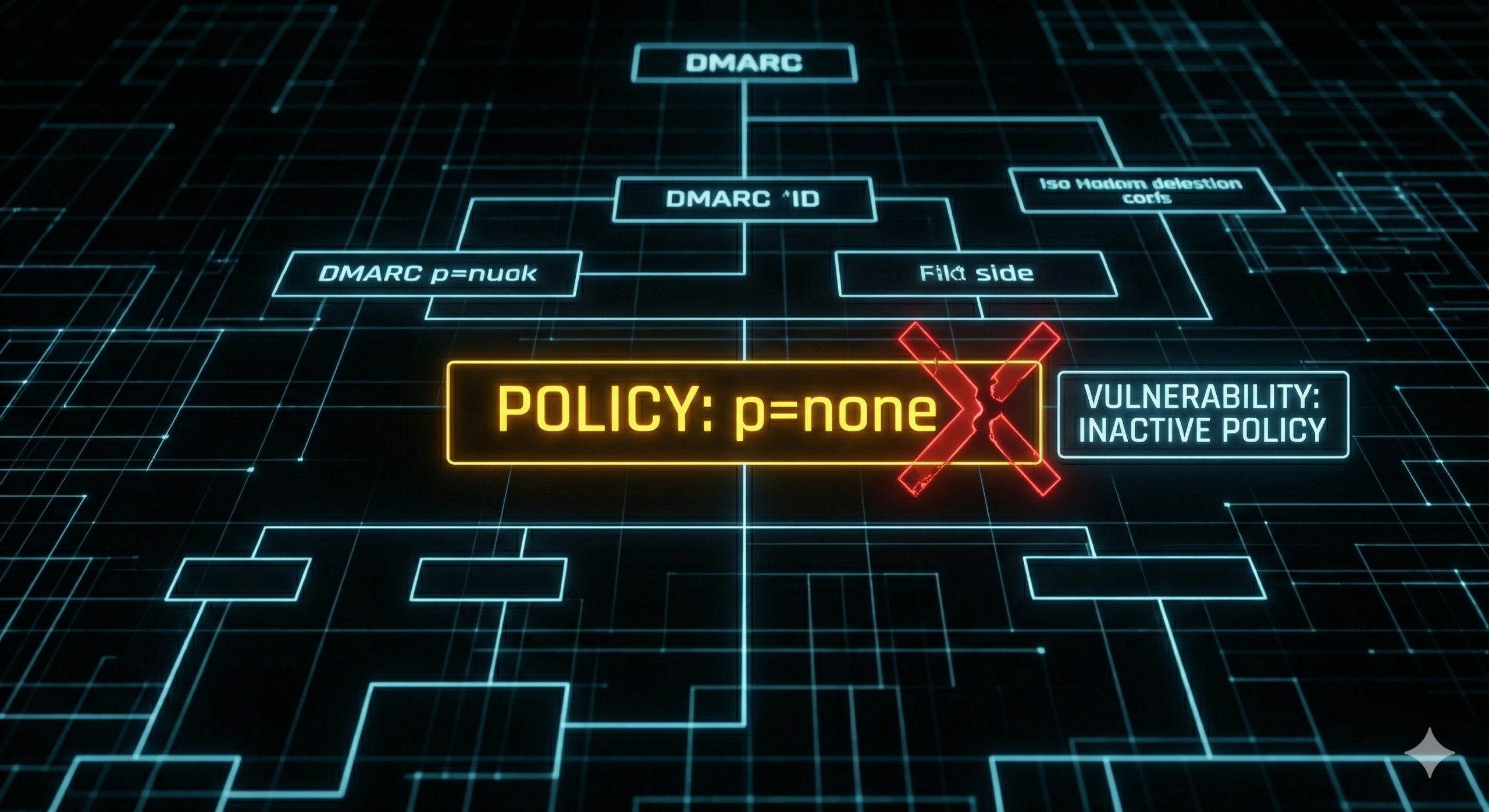
The "p=none" Trap: Why Your Current DMARC is Useless